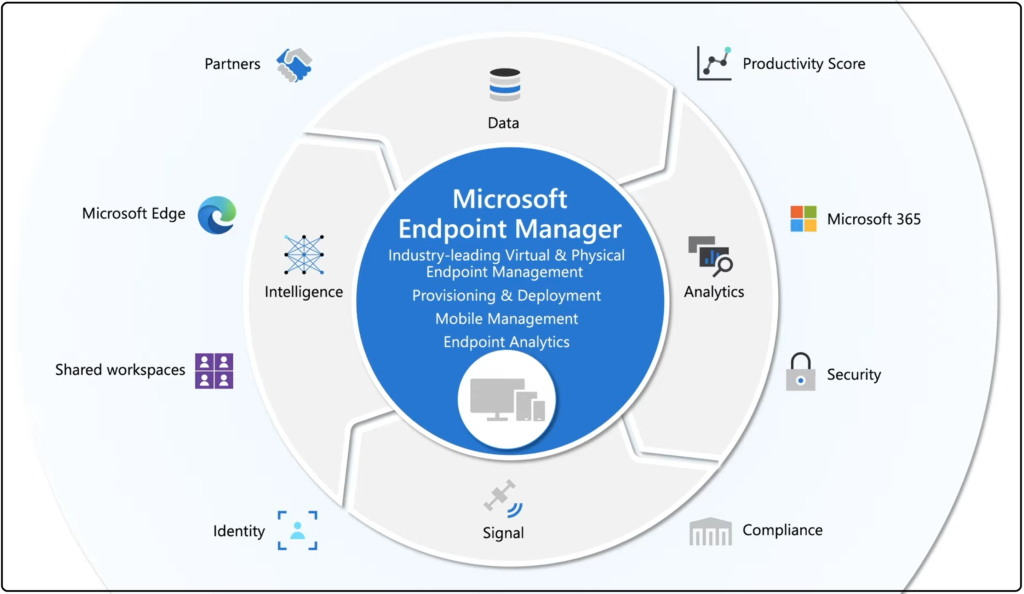
Unified endpoint management (UEM) is used in organizations where devices require a unified console to be managed and secured. It combines enterprise mobility management (EMM), mobile device management (MDM) and client management, and analyses a variety of devices and platforms to provide IT departments with cross-platform security and management, thus broadening the scope of device administration and data protection.
Replacement of EMM, MDM and Client Management Tools by UEM
macOS and Windows 10 devices controlled by MDM cannot assist with traditional desktop applications, while client management systems can help in such cases. Some business organizations have shifted to UEM solutions while still keeping MDM workflow as a base. To adapt to the UEM market, several companies have entirely changed their client management approach and framework.
The highlights of engaging UEM include:
- It can manage, control, configure and monitor macOS, Android, iOS, Windows and Linux devices from one console.
- Application management, device management, data security and compliance, all use a single-handed approach.
- The end-user support allows enhanced visibility over network devices.
- When integrated with ITSM tools, the service level agreement resolution (SLA) time and the offers improve productivity.
Features of UEM you need to know
The evolution of UEM has led the market to include both purpose-built UEM solutions and those that have evolved from the more traditional endpoint management solutions. Below are some features of UEM that an organization needs to know:
Device Compatibility
Endpoint management has to support all types of operating systems like Windows, Mac, Linux, etc. The range of supported endpoint types varies with each solution, so ensure the complete device fleet is covered before purchasing. Organizations need to ensure that all of their employee’ devices support the chosen solution because BYOD users have to set up their devices by themselves.
Centralized Management
The management console is centralized, allowing the organizations to remotely monitor and troubleshoot all endpoints. The features offered by a management console are as follows:
- Distribution of software and policy update configuration
- Role-based access configuration
- Overview of devices connected to the network
- New user and device enrollment
- Compliance reporting
- Remote application and content distribution
- User authentication
Before giving access to any application, multi-factor authentication requires users to authenticate their identity in two or more methods. The three methods can include a PIN, an authenticator app, and a fingerprint scan.
Application Isolation
Application isolation is crucial if the organization is implementing unified endpoint management solution across a BYOD device fleet. Employees can utilize this functionality to divide their personal and work applications and safely use them on the same device.
Integrations
For faster provisioning and patch management, a solid UEM solution will interface seamlessly with any existing endpoint management tools one may have, as well as any third-party apps such as Active Directory, Google Workspace, and Microsoft 365.
Endpoint Security
UEM solutions provide insights for device usage and help configure policies. They also help implement security measures to protect the networks’ devices and enable organizations to implement security through powerful integrations.
Choosing the right UEM solution
Organizations opting for a UEM solution need to analyze their demand based on the endpoints they have. They can check into the corresponding vendors offering similar features and select one that would best match their needs after examining their budget and need for a unique set of network requirements.
Reference links:
- https://blog.tbconsulting.com/importance-of-endpoint-management-and-security
- https://dzone.com/articles/the-what-why-and-how-of-unified-endpoint-managemen
- https://expertinsights.com/insights/what-is-unified-endpoint-management-uem-and-how-does-it-work/

James is a great tech-geek and loves to write about different upcoming tech at TechyZip. From Android to Windows, James loves to share his experienced knowledge about everything here.

Leave a Reply